
I haven’t had a “case of the Mondays” for a while. As a self-proclaimed optimist, there isn’t much about the start of the week that can bother me as long as I prepare for it. Unfortunately, I was only so prepared for the two text messages I received on Monday morning.
“###### is your Twitter login code” read the start of these messages, timestamped almost exactly an hour apart from one another at 8:36 and 9:34 a.m.
I’d been heading downstairs for breakfast at the time the first text message was sent, and in the midst of collecting my notes and books for lecture, I hadn’t put much thought into why I received the text. The second time around, as I was walking to class, I was reminded what purpose these messages had in the first place.
Besides requiring a login password, Twitter can send you a mobile verification code to enter every time you log-in via an unfamiliar server. This ensures that you are indeed the true user of your account–all you have to do is glance down at your phone and type in a six-number sequence to access it.
Someone, or something, was trying to hack my Twitter account.
Feeling uneasy, I checked out my other social media platforms. Everything else was untouched, though relief dissipated quickly when I tried logging into my bank account. It was locked, apparently because I’d tried logging in one too many times.
And all of the sudden, I’d had better Mondays.
In an attempt to see where I could have taken a cyber-security misstep, I contacted Assistant Professor Sharon Goldberg in the Computer Sciences department. Recalling my experience, she pointed out a more-obvious-than-you’d-think problem: I used the same password for my bank and Twitter accounts.
“Your bank password is holy,” Goldberg said.
While online accounts don’t all fall into just one category of importance, critical accounts, like your bank or StudentLink, ought to have specific and strong passwords, she said.
But how did I get attacked in the first place? That’s hard to determine, but it usually involves taking advantage of insecure codes and inserting malware or accessing and exploiting your data from a remote location. It could come down to what you share publicly on social media, like your birthdate or email. You might feed hackers hints to crack your passwords with every tidbit of information you put out there and before you know it, they have taken all of your information and the worst part is that sometimes this could give them access to even you business’s data. This is exactly why experts are always recommending professional data management and security services like those offered by EATEL managed wifi. You can also visit sites like https://tvit.net/managed-it-services-in-cambridge-id/ to hire managed IT service to protect your data.
“There’s no real way to go back” after a possible online breach, says Goldberg–but you can move forward. Change your password immediately, she says, but, more importantly, reset security questions and make sure recovery email addresses and phone numbers weren’t compromised in the hacking process.
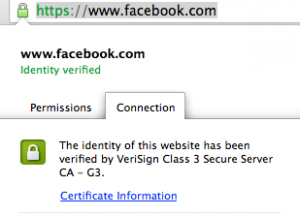
Another thing to look out for: be aware of how you are surfing the web. That means making sure the website is secure–if there’s a lock icon at the front of the status bar, you are. This indicates that the connection between your computer and the server is encrypted. Any hacker who attempts to sit in on the server will find themselves unable to access your information.
“They can’t actually read what traffic you’re sending,” Goldberg said.
If you click on the lock, you’ll notice the website’s SSL certificate (VeriSign, Thawte, Symantec, to name a few) authorizes the website’s credibility.
Because our lives are so intertwined with the Internet, we are sometimes unaware of how vulnerable we are. You can’t control everything, but you can take the steps to secure your online presence. Twitter’s mobile verification module may be the sole reason my accounts weren’t completely breached–I’ll be using Facebook’s from now on, as well. Get anti-malware and anti-virus software. Use secure servers like colocation (get it here) whenever possible–and at all times when handling sensitive information like card numbers, passwords, and other personal information. And for goodness sakes, don’t use “password” as your password.
There’s protection out there, kids. Use it.
As cyber-security threats increase, knowledge is power. Coincidentally, it’s National Cyber Security Awareness Month. Take some time to read up on how you can better secure your digital data. I suggest visiting websites like https://www.fortinet.com/solutions/enterprise-midsize-business/network-access/application-access to get all the information you need.

